How It Works
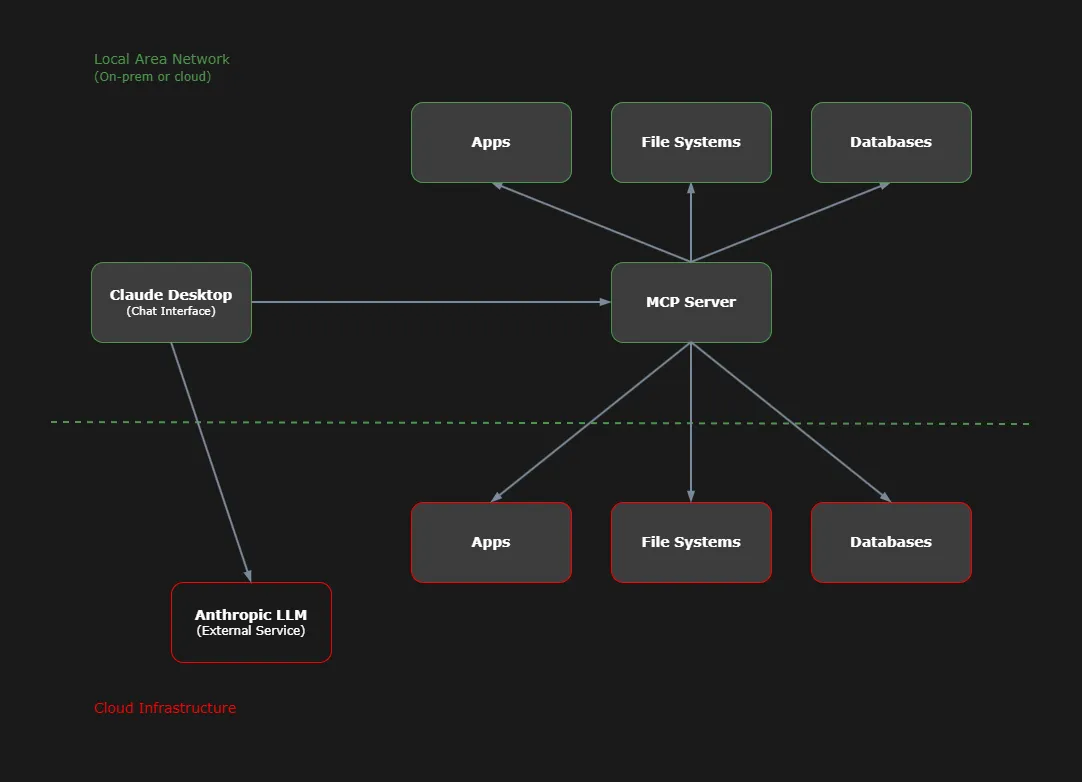
The AI Analyst for Manufacturing uses MCP (Model Context Protocol) servers that bridge the gap between Claude Desktop and your data, enabling conversational analytics that works with your existing infrastructure—whether LAN-based, cloud-based, or a mix of both.
MCP-Based Architecture
The Flow
Understanding how data moves through the system clarifies both the capabilities and the boundaries of a RedStem implementation.
User Queries in Claude Desktop
The user interacts with Claude Desktop, a chat interface that connects to both Anthropic's language models and your MCP server.
MCP Server Receives Request
The MCP server—running within your infrastructure—receives the request via the Model Context Protocol. This server has controlled access to your data sources, whether on your LAN or in the cloud.
Server Accesses Your Data
The MCP server queries your data sources—whether internal databases, file systems, legacy applications on your LAN, or cloud-based systems like ERP platforms. Data access is controlled; nothing is migrated or duplicated.
Response Processed and Returned
Retrieved data is structured and returned to Claude Desktop, where Anthropic's language model can process, summarize, or analyze it based on the user's request.
User Sees Result
The response appears in the Claude Desktop chat interface—aggregated information, generated reports, or actionable insights, all derived from your data.
Security & Data Residency
Your data stays where it is—LAN or cloud. The MCP server runs within your infrastructure and accesses data according to permissions you control.
Data Stays in Place
Whether your data lives on LAN servers, in cloud platforms, or both, MCP servers query it where it resides. No migration or duplication required.
Controlled Access
The MCP server operates with the access permissions you define. It queries only the systems you authorize, respecting existing security boundaries and authentication requirements.
Honest About External Connections
Claude Desktop connects to Anthropic's language model services to process requests. This is an external connection. RedStem does not claim "zero cloud interaction"—that would be misleading.
Security-First Posture
Every implementation prioritizes security boundaries and data residency. Deployments are designed to minimize external exposure while enabling AI-assisted capabilities.
Why This Works for Non-Cloud-Native Firms
Many SMB manufacturers operate in constrained environments. Moving to fully cloud-based systems creates legitimate concerns:
- Security and compliance requirements that favor controlled data residency
- Legacy systems that are costly or impractical to replace
- Proven workflows that would be disrupted by wholesale platform changes
- Limited IT resources for managing complex cloud migrations
MCP-based architecture respects these constraints. It works with your existing infrastructure rather than requiring you to abandon it. AI-assisted capabilities are added as a layer, not as a replacement.
This approach reduces risk, preserves institutional knowledge embedded in current systems, and enables incremental adoption rather than disruptive transformation.
MCP architecture also supports firms that have partially migrated to cloud systems, connecting both environments through a single interface.
Discuss Implementation
Questions about how MCP architecture applies to your specific infrastructure?